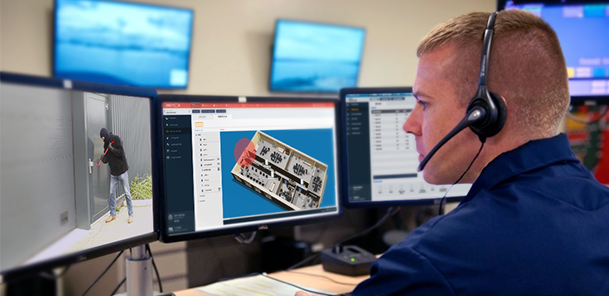
Did you know that your RFID access card can be copied by anyone in a matter of seconds?
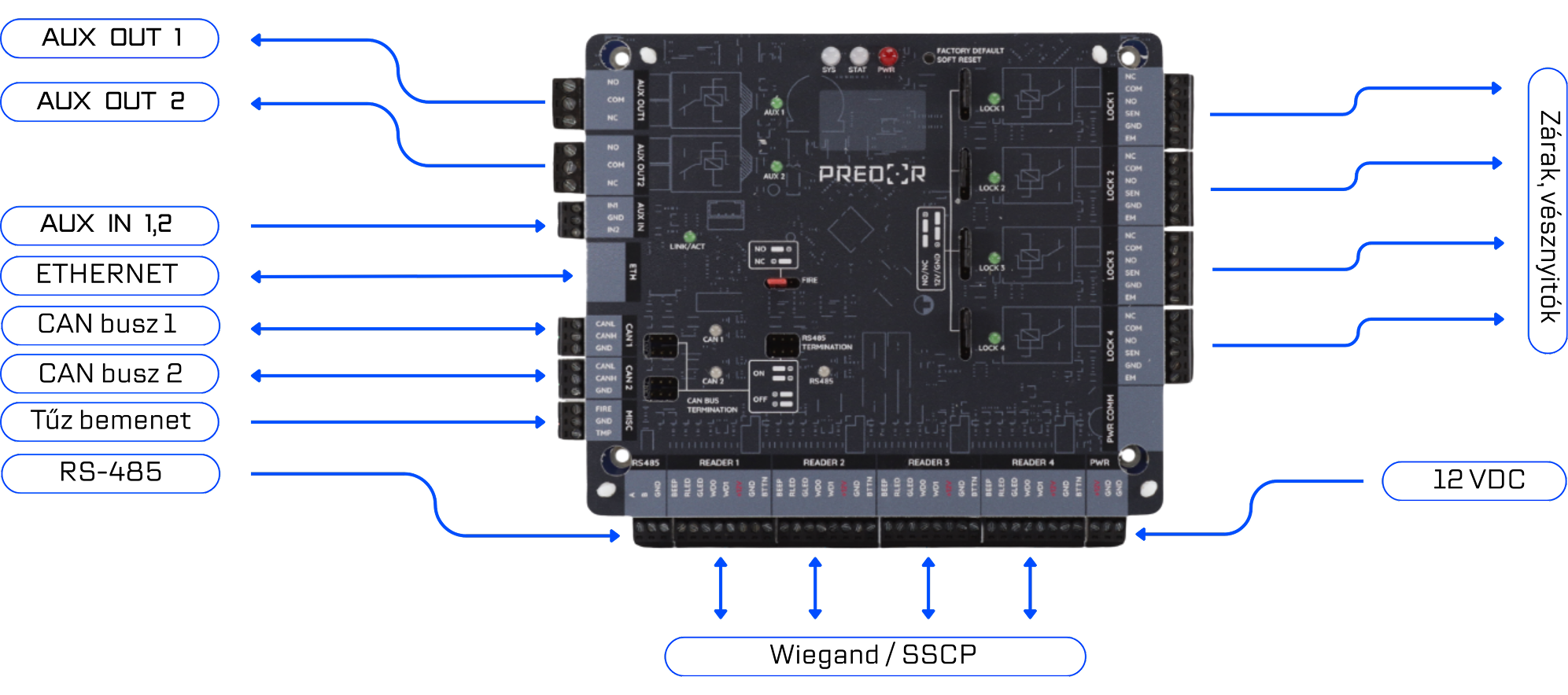
In this video, we show how easy it is to copy, emulate, and duplicate RFID cards with a Flipper Zero. We want to draw attention to the weak points of access control systems and the importance of NIS2. The Predor system provides end-to-end secure communication.